Lilac Wolverine, a cybercrime group based in Nigeria, has been accused of targeting and defrauding many businesses in the United States of America and western Europe through Business Email Compromise (BEC), a fraudulent scheme involving the use of compromised emails.
According to Abnormal Security, a behavioural AI-based security platform in San Francisco, California, USA, members of the group compromise their victims’ personal email accounts. They then send out emails in large batches, targeting everyone on each compromised account’s contact list. In the emails, the fraudsters use “emotionally charged themes” to prevail on unsuspecting victims to purchase gift cards for “friends and relatives who are in need”.
They mostly cite the “untold hardship” caused by the Covid-19 pandemic when soliciting help from their targeted victims.
READ ALSO: Tweep Who Accused Innoson of Selling Fragile Vehicles Deletes Account
Through the scheme, Lilac Wolverine members are able to target hundreds of recipients in a single campaign. Instead of targeting businesses, the group goes after personal email accounts, especially those hosted on AOL, Yahoo, BellSouth, Verizon, and Rogers webmail services.
Lilac Wolverine’s extremely high attack volume also makes it one of the most prolific cybercrime syndicates presently.
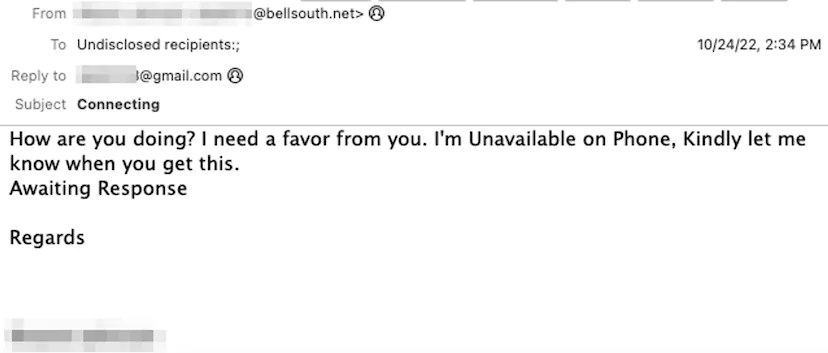
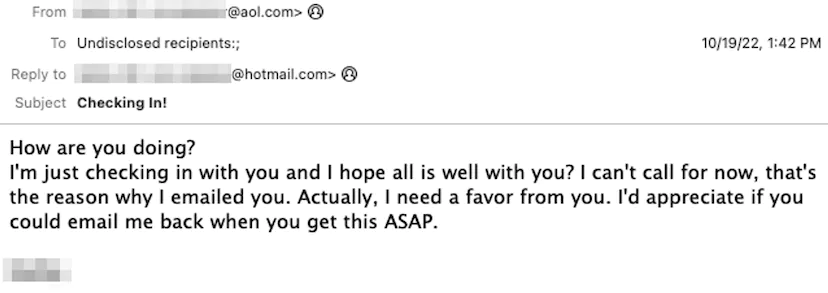
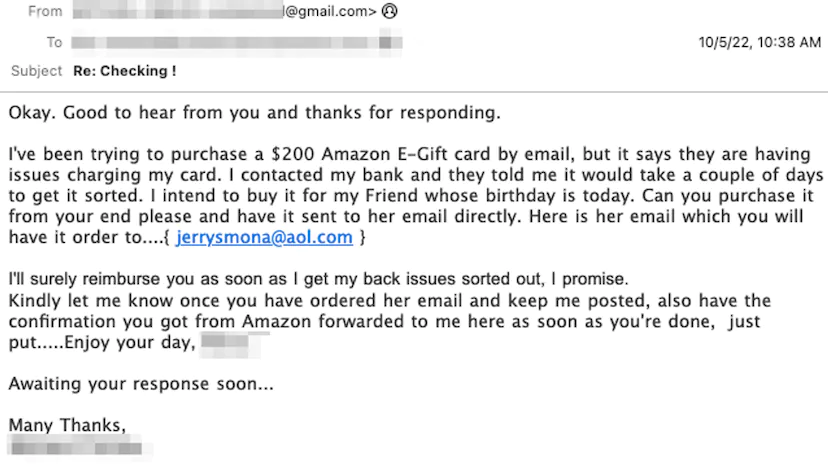
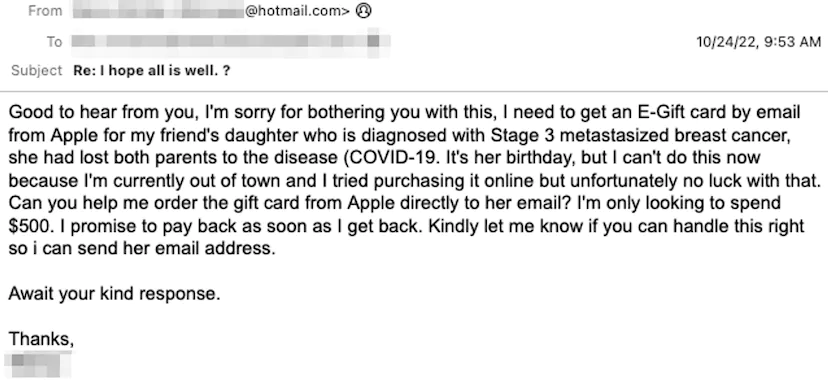
Once the targets respond to the emails, the Lilac Wolverine members manipulate them into purchasing gift cards on their behalf, promising to pay them back.
In May, the FBI said more than $43 billion had been lost through Business Email Compromise and Email Account Compromise scams since 2016.
READ ALSO: Senator Albert Bassey Sentenced to 42 Years in Prison for Money Laundering
“The BEC scam has been reported in all 50 states and 177 countries, with over 140 countries receiving fraudulent transfers,” said Paul Abate, FBI’s deputy director.
“Lilac Wolverine takes advantage of this broader target pool by launching some of the largest campaigns we see from any BEC threat group out there.
“Lilac Wolverine’s extremely high attack volume makes the group one of the most prolific we track today. Rather than sending messages directly from the accounts they compromise, Lilac Wolverine copies the accounts’ contacts to use in the next stage of their attack.”
Subscribe
Be the first to receive special investigative reports and features in your inbox.