Half the available Google Chrome extensions are capable of harming their users, Incogni, a data protection company in Netherlands, has revealed.
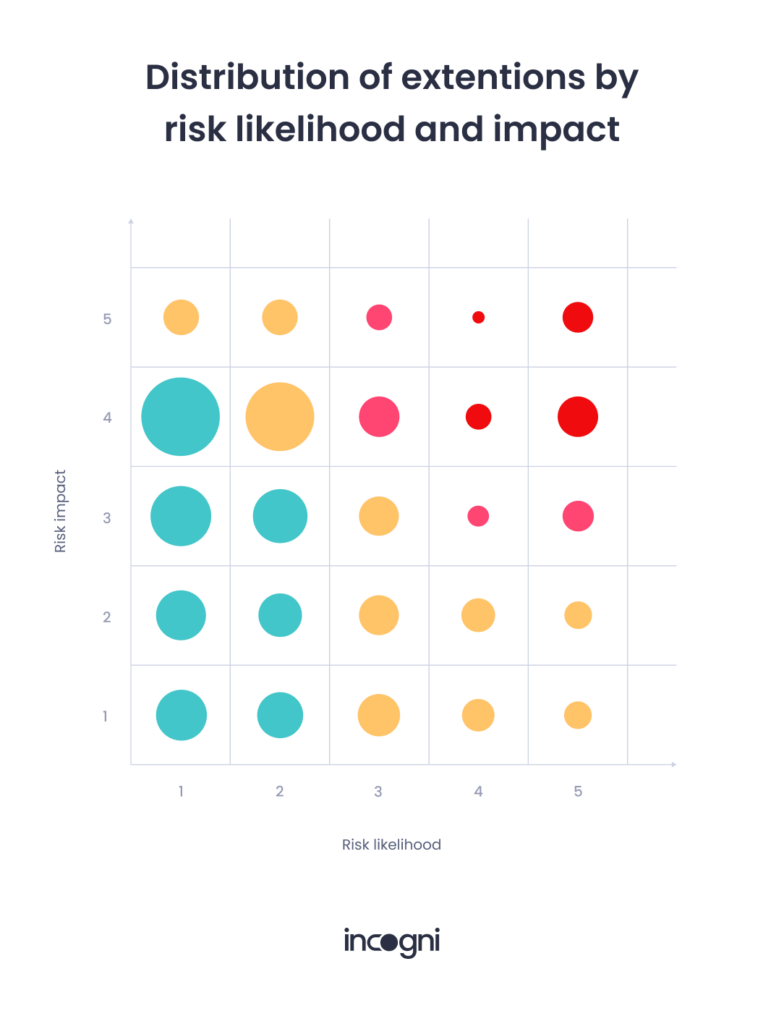
Its research, made available to FIJ on Wednesday, showed that after reviewing 1,237 extensions, 602 (48.66 percent) of them had a high or very high risk impact.
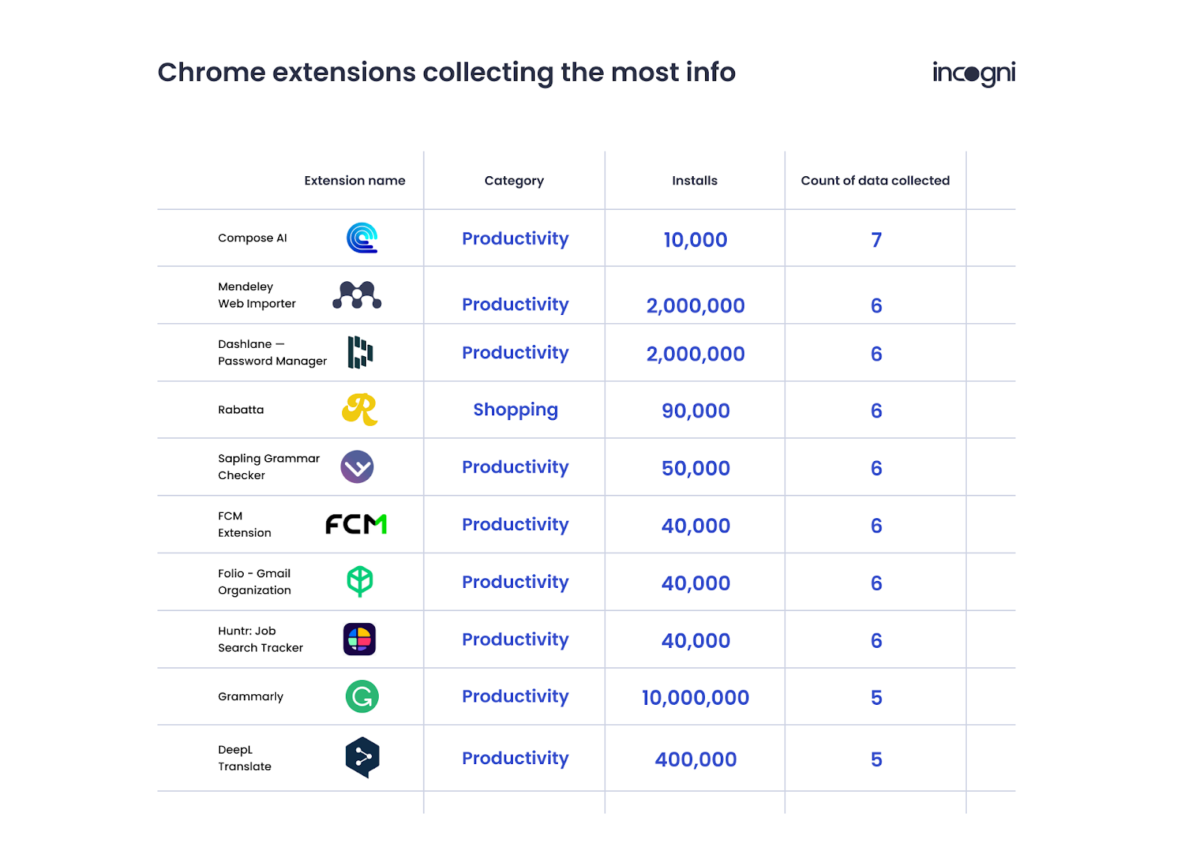
It also revealed that 334 (27 percent) of the sampled extensions collect users’ data. Amongst its findings was that extensions in the ‘Shopping’ category were the most potentially harmful, while those used for writing collect the most data.
The company said, “The safest extensions have a low Risk Impact and low Risk Likelihood, while the most dangerous score highly on both measures. The vast majority fall somewhere in between these extremes and it’s up to the user to decide if they’re comfortable installing a given extension.
READ MORE: 5 Google Chrome Extensions Are Silently Stealing Data From Nigerians
“Risk Impact won’t change without the user knowing, since the extension would have to request additional permissions, but Risk Likelihood can change without notice, for example when an extension changes hands.”
The distribution below shows the proportions of extensions studied that are generally considered safe (teal), that should be installed with caution (yellow), generally avoided (pink), or that are not recommended (red).
The company further said, “Some extensions truly can’t function without certain permissions, even scary ones like clipboard read and browsing data. This is why it’s important to only use extensions from trusted developers. A trusted developer is one with a history of problem-free software development and high user ratings.
“Seeking out trusted developers is neither easy nor foolproof, though. A previously above-board developer can turn bad actor, reviews can be bought or faked, and extensions can be compromised through no fault of the developer.
“Doppelganger extensions also complicate things. You might think you’re installing a tried, tested, and trusted extension when really it’s a malicious counterfeit. These are easy to fall for if you’re not very careful to match the extension and developer names exactly.
READ ALSO: Ransomware Is Dangerous. Here’s How to Protect Your Data and Networks From It
“Finally, there’s a risk to downloading High Risk Impact extensions even from verified and trusted developers. Extensions, like any other proprietary software, can change hands without the user being made aware. You grant permissions to the extension, not its developer. A less-than-trustworthy company could then acquire the developer, publisher, or code base and do as it pleases with your data.”
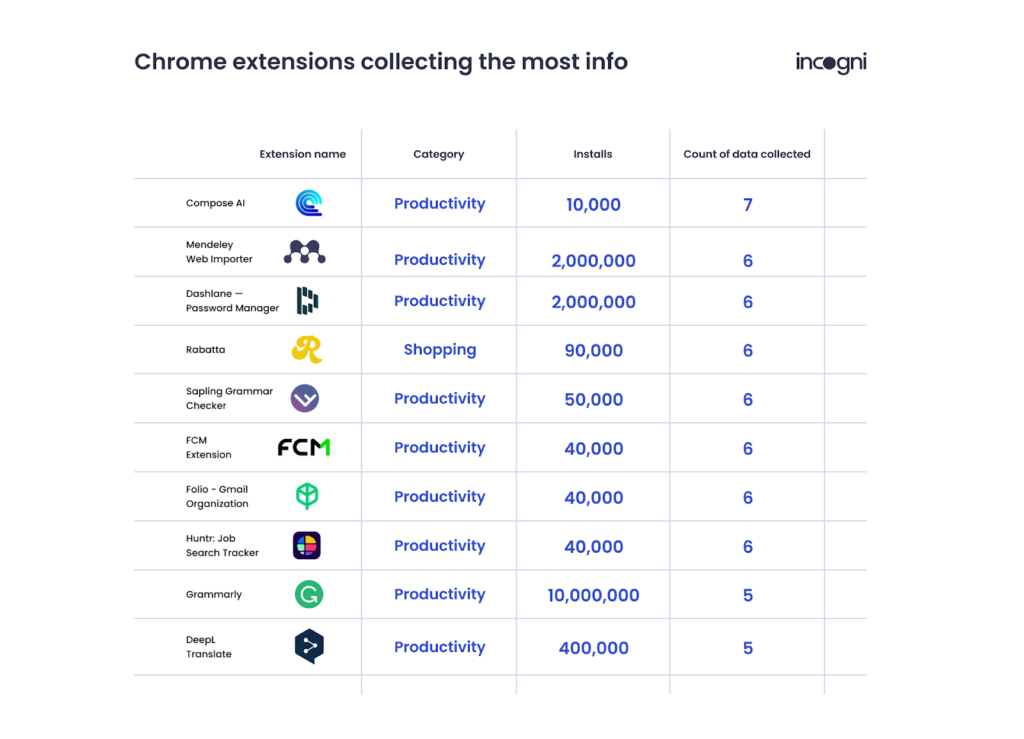
Incogni found nine extensions that collect the most user data, and represented them in the table above.
Subscribe
Be the first to receive special investigative reports and features in your inbox.